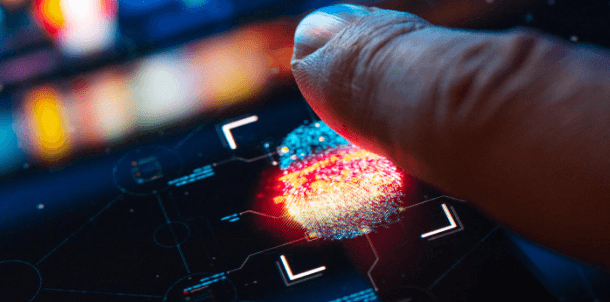
Biometric technology is evolving toward integrated, context-aware authentication that blends physiological, behavioral, and ambient signals. Systems will enable seamless, multi-device access while embedding privacy-by-design and granular consent. Governance, risk assessment, and independent auditing will shape deployment across sectors. The trajectory emphasizes fairness, explainability, and modular policy updates to sustain interoperability. As data-driven assurances rise, stakeholders must weigh efficiency gains against potential inference risks, leaving the key questions open for sustained examination.
What Biometrics Are Evolving Toward in Everyday Life
Biometrics are evolving from single-factor, device-bound identifiers toward integrated, context-aware systems that seamlessly blend physiological and behavioral signals with ambient data. This trajectory supports pervasive authentication across devices and environments, enabling calmer user experiences and adaptive access controls.
The privacy evolution emphasizes granular consent and transparency, while security implications focus on resilience, multi-factor fusion, and robust anomaly detection to deter spoofing and unauthorized inference.
Balancing Privacy, Ethics, and Security in Next-Gen Biometrics
Balancing privacy, ethics, and security in next-generation biometrics requires a principled synthesis of user autonomy, transparent governance, and robust technical safeguards. Data-driven analyses point to measurable privacy tradeoffs and minimized inference risk as core targets. Forward-looking frameworks emphasize consent frameworks, modular policy updates, and verifiable security proofs, enabling freedom to innovate while preserving individual rights and accountable system behavior across diverse deployments.
Real-World Use Cases Transforming Industries and Services
Real-world deployments of biometric technology are already reshaping operations across healthcare, finance, retail, and public services, driven by improved accuracy, speed, and user experience.
Data-driven consent frameworks, cross-border interoperability, and privacy-by-design principles enable scalable, compliant adoption.
Ethical deployment hinges on transparent governance, measurable outcomes, and continuous monitoring, empowering stakeholders and sustaining trust while fueling innovative, data-enabled service models.
Designing Responsible Biometric Systems for a Trustworthy Future
Designing responsible biometric systems requires a principled, evidence-based approach that foregrounds privacy, accuracy, and fairness from inception.
The framework emphasizes privacy by design and consent centric architectures, enabling transparent governance and user empowerment.
Data-driven evaluation informs risk mitigation, model updates, and accountability.
A trustworthy trajectory relies on independent auditing, standards alignment, and scalable, interoperable solutions that preserve freedoms while enhancing security and societal benefit.
See also: kamaikendra
Frequently Asked Questions
How Will Biometrics Handle Cross-Border Data Transfers?
Cross-border transfers will rely on data localization frameworks and robust cross-border compliance measures, with biometric systems adopting standardized privacy-by-design controls, auditable data flows, and reciprocal enforcement, enabling secure, freedom-preserving interoperability while meeting evolving regulatory demands and risk assessments.
What Are the Risks of Biased Biometric Systems?
Biometric systems risk bias issues, leading to unequal outcomes and discrimination. They must be evaluated with transparent metrics, diverse datasets, and ongoing auditing to ensure equal access; mitigation strategies should prioritize accountability, fairness, and data governance for a freer future.
Can Biometrics Be Hacked or Spoofed Easily?
Like a beacon in the fog, biometrics can be hacked but risks are declining. The assessment shows biometric deception persists with spoofing resilience improving through multi-factor designs, liveness checks, and continuous authentication, supported by rigorous, data-driven risk modeling.
Will Biometrics Replace Passwords Entirely?
Biometric adoption will not fully replace passwords, but will substantially reduce reliance on them. The trajectory emphasizes multi-factor, risk-based use. Privacy implications require strong governance, transparent data handling, and robust cryptographic protections to preserve user autonomy and freedom.
How Transparent Are Biometric Data Collection Practices?
Biometric data collection practices appear surprisingly transparent, though privacy myths persist; consent complexity challenges persist as institutions publish dashboards, audits, and standards. The analysis emphasizes data minimization, verifiable provenance, and ongoing, data-driven governance for freedom-minded stakeholders.
Conclusion
As biometric systems mature, they converge into a chorus of context-aware signals, harmonizing identity, behavior, and environment. Data-driven risk models illuminate pathways to fair, privacy-preserving access across devices and domains. Transparent governance and independent audits act as lighthouses, guiding deployment while imposing accountability. The trajectory is rigorous and forward-looking: a resilient, interoperable ecosystem that empowers users, reduces inference risk, and sustains trust through modular policy updates and ethical stewardship. The future hinges on responsible innovation guided by measurable, verifiable safeguards.